Meet-in-the-middle – cryptanalysis optimization technique
Applying the meet-in-the-middle approach reduces the time complexity of certain attacks by…
Signature aggregation – combining multiple signatures
The BLS scheme enables the fusion of distinct cryptographic proofs into a…
Time locks – delayed transaction execution
Implementing conditional time-based controls enables deferred processing of critical actions, ensuring they…
Social engineering – human factor vulnerabilities
Recognize that deceptive tactics such as pretexting and phishing rely on exploiting…
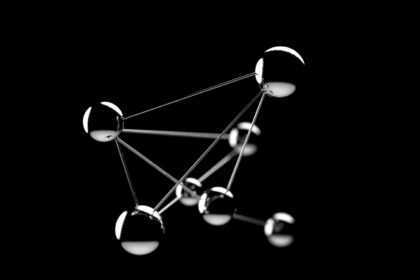
Peer-to-peer networks – direct communication protocols
Utilizing decentralized systems enables nodes to interact without intermediaries, enhancing efficiency and…
Protocol design – secure communication frameworks
TLS and SSH remain foundational standards for encrypted data exchange, demonstrating critical…
Exploit development – weaponizing vulnerabilities
Manipulating a buffer overflow requires precise insertion of shellcode alongside a carefully…
Hash functions – one-way mathematical transformations
Secure verification relies on irreversible mappings that convert input data into fixed-size…
Malware analysis – understanding malicious software
Start by combining static and dynamic techniques to dissect harmful programs effectively.…
Network topology – blockchain node arrangements
Optimal distribution of archive, full, and light participants within a decentralized system…